How to write your Company Equipment Checkout Form
We include this 2 page template with Contractors Contract Pack and the Proposal Kit Professional. You will get more content and software automation for data merging, managing client documents, and creating proposals with line item quoting with a Contract Pack or the Professional.
 DOWNLOADABLE, ONE-TIME COST, NO SUBSCRIPTION FEES
DOWNLOADABLE, ONE-TIME COST, NO SUBSCRIPTION FEES What Our Clients Say
What Our Clients SayI have written proposals a few years back and it was great to have a template to remind me of the critical components that needed to be included. The kit helps to win business, but at the same time it helps to protect my business by including the critical contractual components of the proposal."
1. Get Contractors Contract Pack or the single template that includes this business contract document.
We include this Company Equipment Checkout Form in editable Word format that can be customized using your office software.
2. Download and install after ordering.
Once you have ordered and downloaded your template or pack, you will have all the content you need to get started.
3. Customize the contract template with your information.
You can customize the contract document as much as you need. If you get a Contract Pack or Professional Bundle, you can also use the included Wizard software to automate name/address data merging.
How do you write a Company Equipment Checkout Form document?
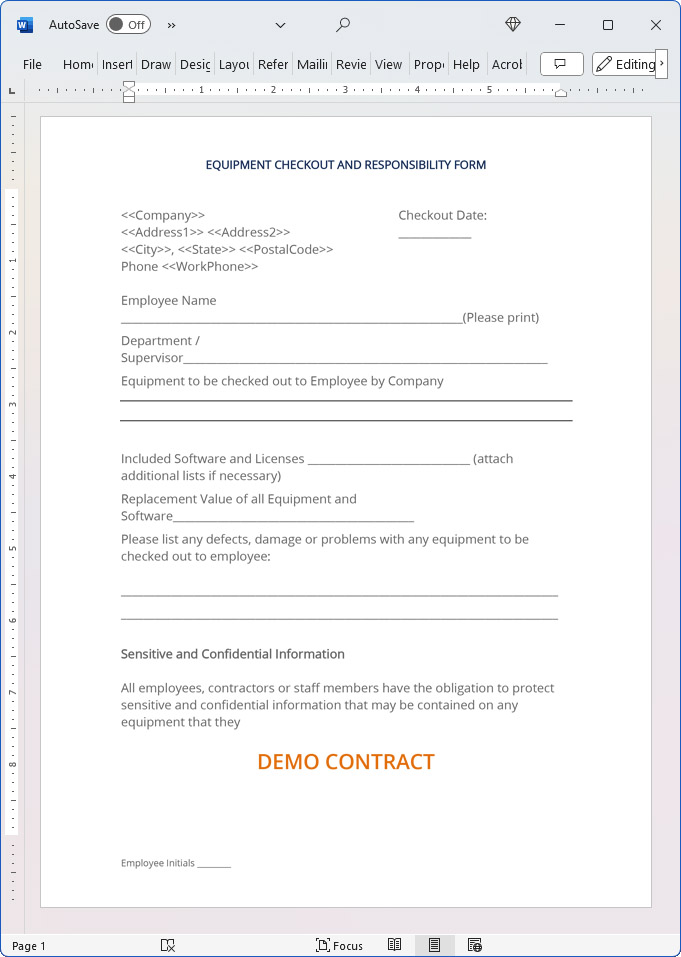
EQUIPMENT CHECKOUT AND RESPONSIBILITY FORM
Company Name
Address Address
City, State Postal Code
Phone Phone Number CHECKOUT DATE:
Employee Name (Please print)
Department / Supervisor
Equipment to be checked out to Employee by Company. Included Software and Licenses (attach additional lists if necessary). Replacement Value of all Equipment and Software.
Please list any defects, damage or problems with any equipment to be checked out to employee:
Sensitive and Confidential Information
All employees, contractors or staff members have the obligation to protect sensitive and confidential information that may be contained on any equipment that they check out or that may be in their possession. All mobile computing users who make use of wireless networks must use VPN encryption protocols to send or transmit sensitive or confidential information in any form. No employee, contractor or staff should ever access an internal company network resource without being secured by VPN encryption protocols, as all Company internal networks, network resources or other internal assets shall be deemed sensitive and confidential information. The Company also reserves the right to pursue legal remedy for damages incurred as a result of an employee's violation.
For additional information, consult the Company Wireless Network and Mobile Computing Policy. Certain illegal activities will require that Company immediately notify or comply with the proper authorities upon discovery. The Company reserves the right to examine any user's equipment, whether personally owned or Company owned, that accesses Company Email Account(s), Web Logs, Chat Logs, Networks, Access Points or any other information passed through Company resources or Network, or stored on Company computers, at any time and without prior notice. Company is not responsible for users who display, store, or otherwise transmit any personal information such as passwords, banking information, credit card numbers, social security or tax ID numbers, or make use of Internet "passports" or "wallets" while using Company equipment.
Company shall not be held liable for damages resulting from any loss of such information, abuse by other parties, or any consequential loss of personal property or injury resulting from the storage or loss of such information. The practices described in this Equipment Checkout and Responsibility Form are current as of Current Date. Company reserves the right to modify or amend this policy at any time.
Effective Date: Current Date
I hereby declare that I have read and fully understand my duties and obligations set forth in the above Equipment Checkout and Responsibility Form for Company Name, and I will uphold these duties and obligations at all times. EXECUTED as of the date first written above. Signature: Date when the contact was signed.
Employee Initials
 4.7 stars, based on 839 reviews
4.7 stars, based on 839 reviewsKey Takeaways
- The Company Equipment Checkout Form is available as a ready-to-edit template.
- The Contract Packs and Professional Bundle include many related agreements and documents.
- You can automate financials and data merging into contracts using a Contract Pack or Professional Bundle.
- You can also create business proposals and integrate your contracts using the Professional Bundle.
- There are no ongoing subscription fees. You get lifetime unlimited use.
 Ian Lauder has been helping businesses write their proposals and contracts for two decades. Ian is the owner and founder of Proposal Kit, one of the original sources of business proposal and contract software products started in 1997.
Ian Lauder has been helping businesses write their proposals and contracts for two decades. Ian is the owner and founder of Proposal Kit, one of the original sources of business proposal and contract software products started in 1997.By Ian Lauder
 Published by Proposal Kit, Inc.
Published by Proposal Kit, Inc.Disclaimers
Proposal Kit, Inc. makes no warranty and accepts no responsibility for the suitability of any materials to the licensee's business. Proposal Kit, Inc. assumes no responsibility or liability for errors or inaccuracies. Licensee accepts all responsibility for the results obtained. The information included is not legal advice. Names in use cases have been fictionalized. Your use of the Company Equipment Checkout Form template and any purchased packages constitutes acceptance and understanding of these disclaimers and terms and conditions.


 Cart
Cart
 Facebook
Facebook YouTube
YouTube X
X Search Site
Search Site