Open Systems Interconnection Reference Model Form
We include this editable document in the Proposal Kit Professional. Order and download it for $199. Follow these steps to get started.
 DOWNLOADABLE, ONE-TIME COST, NO SUBSCRIPTION FEES
DOWNLOADABLE, ONE-TIME COST, NO SUBSCRIPTION FEES
Key Takeaways
- One-time License, No Subscriptions: Pay once and use Proposal Kit forever-no monthly fees or per-use charges.
- Built for Business Projects: Start with a proven Open Systems Interconnection Reference Model Form and tailor sections, fields, and branding for your day-to-day project work.
- Instant Access: Download immediately and open the document right away-no waiting, no onboarding delay.
- Project-Ready Structure: Use a ready, professional layout for real-world project tasks (checklists, forms, analysis pages) so teams can execute consistently.
- Fully Editable in Word: Edit everything in Microsoft Word-swap text, add/remove sections, and apply your logo/colors without special skills.
- Step-by-Step Wizard Help: The Proposal Pack Wizard guides you with training/help and keeps you moving-no getting stuck on formatting or assembly steps.
- Wizard Data Merge & Project Management: Let the Wizard manage projects and merge recurring data (company/client names, addresses, dates) across your project documents.
- Included in Proposal Kit Professional: Available exclusively in the Proposal Kit Professional bundle.
 What Our Clients Say
What Our Clients SayI have been using this system for over 8 years and it is the best that money can buy. It paid for itself many times over every year. I have no reservations recommending this software. This is the best buy on the internet. Don’t be fooled by pretenders."
Inroads, LLC
1. Get Proposal Kit Professional that includes this business document.
We include this Open Systems Interconnection Reference Model Form in an editable format that you can customize for your needs.
2. Download and install after ordering.
Once you have ordered and downloaded your Proposal Kit Professional, you will have all the content you need to get started with your project management.
3. Customize the project template with your information.
You can customize the project document as much as you need. You can also use the included Wizard software to automate name/address data merging.
Use cases for this document
BrightForge Robotics tames its plant-floor network by mapping every layer
The Challenge
Production at BrightForge Robotics kept stalling from ARP storms, duplex mismatches, and unclear ownership among vendors' network devices; machine builders pushed for quick fixes while IT needed a defensible plan that covered error control, routing addressing, and how data flows from sensors to analytics using the TCP/IP model.
The Solution
Lena Ortiz, the lead architect, used the OSI reference document to align stakeholders: layer one physical for media types and full duplex half duplex settings; layer two data link for Ethernet PPP choices, MAC address plans, error detection correction, and flow control error handling; layer three network for IP addressing, routing protocols, address resolution protocol, maximum transmission unit, and packet fragmentation reassembly; layer four transport for osi connection oriented transport with transmission control protocol vs user datagram protocol; layer five session for session establishment maintenance termination; layer six presentation for encryption decryption; and layer seven for application protocols like smtp ftp dns and remote file access. Proposal Kit produced supporting documents: the RFP response narrative with the RFP Analyzer, a training guide, a cutover runbook via the AI Writer, and a bill of materials with line-item quoting.
The Implementation
Workshops translated PDU SDU boundaries into cabling, VLANs, and QoS policies; address resolution protocol tuning and frame design reduced broadcast noise; routers were set to enforce MTU consistency to prevent fragmentation; switches were locked to full duplex; and a pilot line proved error control and flow control mechanisms under load before rollout, with Proposal Kit generating executive updates and a risk register alongside the project management documents.
The Outcome
Unplanned downtime dropped, commissioning sped up, and procurement approved a clean handoff because the layered plan made responsibilities, costs, and testing traceable end-to-end.
Harbor Valley Health secures cloud EHR access with layered controls
The Challenge
The clinic's EHR move to the cloud exposed gaps in encryption, DNS dependencies, and legacy file exchanges; clinicians saw timeouts while the compliance team lacked a clear view of session behavior, error control, and where TLS fits in the stack.
The Solution
The team completed an OSI-based analysis: layer one physical verified fiber and duplex settings; layer two data link detailed MAC address filtering and error detection correction; layer three network defined routing addressing, multicast boundaries, and MTU; layer four transport selected transmission control protocol for records and user datagram protocol for domain name system; layer five session set session establishment maintenance termination for portals; layer six presentation specified encryption decryption using TLS/SSL; layer seven application protocols covered simple mail transfer protocol, file transfer protocol for image transfers, and directory services. Proposal Kit created supporting documents: a security architecture overview and business continuity plan with the AI Writer, a vendor comparison using the RFP Analyzer, and budget estimates through line-item quoting.
The Implementation
Routers and firewalls enforced IPsec where needed, DNS pathways were hardened, SMTP and FTP channels were migrated to secure gateways, MTU and packet fragmentation reassembly behavior were tested across WAN links, and monitoring thresholds tied to PDUs revealed bottlenecks before go-live; Proposal Kit assembled the compliance matrix and stakeholder briefings to align leadership.
The Outcome
Clinicians gained reliable access, auditors received clear evidence of layered controls, and IT reduced incident volume thanks to explicit error control and session policies backed by complete documentation.
Cobalt Ledger accelerates market access with a seven-layer blueprint
The Challenge
A fintech startup, Cobalt Ledger, chased microsecond gains but faced jitter from mismatched MTUs, congested links, and unclear boundaries between application retries and network error control, risking missed trades.
The Solution
Using the OSI document, architect Priya Shah set priorities: layer one physical locked fiber paths to full duplex; layer two data link tuned Ethernet QoS and flow control; layer three network optimized routing addressing and address resolution protocol on exchange cross-connects; layer four transport split traffic-user datagram protocol for multicast feeds and transmission control protocol with maximum segment size tuning and selective repeat sliding window for order flow; layer five session defined reconnect logic; layer six presentation minimized translation overhead; layer seven aligned application protocols with port addressing. Proposal Kit supported the effort by generating a latency study and SLA draft with the AI Writer, parsing colocation vendor requirements via the RFP Analyzer, and building capital and circuit quotes with line-item quoting.
The Implementation
Engineers validated PDU SDU mappings in packet captures, standardized MTU to avoid packet fragmentation reassembly, set deterministic routing, and instrumented error control counters across switches and routers; Proposal Kit assembled executive reports and a change plan that synchronized trading, ops, and compliance teams.
The Outcome
End-to-end latency dropped, reconnect storms disappeared, and investors saw a credible, layered roadmap tying spend to measurable performance gains.
Abstract
This document provides a structured way to map a solution's functions to the OSI model so stakeholders can see how data flows and how each layer interacts. It aligns with standards documents such as ISO/IEC 7498-1 (ISO 7498) and the ITU-T X.200 recommendation and supports clear decisions about communication protocols, interoperability, and risk. By organizing features into a seven-layer architecture with interconnection comments, teams can capture peer-to-peer communication among peer entities, protocol data units (PDU), service data units (SDU), and cross-layer functions such as naming and addressing, security architecture, and a management framework for network management.
Layer 1 focuses on data transmission details: bit synchronization, bit rate control, physical topologies, and transmission modes like full duplex and half duplex. Layer 2 covers node-to-node services with media access control (MAC), logical link control (LLC), frame synchronization, MAC addresses, error detection and correction, and flow control mechanisms across Ethernet or PPP; address resolution can be documented here when relevant. Layer 3 describes logical addressing and packet routing, including IP addressing, routing protocols, router switching, packet fragmentation and reassembly, maximum transmission unit, multicast group management, and quality of service.
Layer 4 sets connection-oriented and connectionless service expectations using the Transmission Control Protocol and the User Datagram Protocol, port numbers, segmentation and reassembly, maximum segment size, error recovery, flow control, and selective repeat sliding window methods. Layer 5 defines session establishment, maintenance, and termination, with dialog controller responsibilities and service point addressing. Layer 6 handles data translation, encryption and decryption, and data compression as a presentation translation layer. Layer 7 lists application protocols and services such as Simple Mail Transfer Protocol, File Transfer Protocol, and the Domain Name System, plus remote file access, directory services, file transfer access management, and a network virtual terminal. Security can be noted at multiple layers, such as IPsec security at Layer 3, MACsec security at Layer 2, and TLS/SSL above the transport layer.
The form also supports a comparison to TCP/IP and the Internet Protocol Suite, showing how data flows through a protocol stack, how port addressing maps to programming interfaces, and how OSI vs TCP/IP choices affect interoperability and connection design.
Use cases include RFPs, cloud migrations, IoT rollouts, network topology redesign, router and switching upgrades, and audits of naming, addressing, and flow control.
Proposal Kit helps teams assemble this analysis quickly using document assembly, automated line-item quoting, an AI Writer that can build supporting documents, and an extensive template library designed for ease of use.
Expanding on the practical use of this form, teams can drive clearer architecture decisions by documenting per-layer requirements end to end. At layer one, physical, specifying media, connectors, and full duplex or half duplex settings reduces deployment risk. The layer two data link entries capture MAC address plans, Ethernet PPP choices, error detection and correction, and flow control error handling.
The layer three network section formalizes routing addressing policies, use of the address resolution protocol, and packet fragmentation reassembly behavior across diverse network devices. Layer four transport clarifies OSI connection-oriented transport expectations and how they align to the TCP IP model. Layer five session defines session establishment, maintenance, and termination rules for reliable resource sharing. Layer six presentation sets formats and encryption decryption needs that affect interoperability and compliance.
The template also encourages documenting protocol data unit and service data unit boundaries (PDU SDU), making how data is encapsulated visible between layers. Mapping application dependencies, such as SMTP, ftp, and DNS, highlights upstream effects on capacity, performance, and security. This level of detail helps forecast impacts of upgrades, guides procurement, and streamlines troubleshooting when incidents span multiple layers.
Proposal Kit can accelerate the creation of these project management documents by assembling consistent layer-by-layer narratives, reusing approved language, and producing companion materials with its AI Writer. Teams can also generate budgets and hardware/software lists with automated line-item quoting, ensuring the OSI analysis ties directly to actionable plans.
Additionally, treating this OSI-layered analysis as a lifecycle artifact helps leadership connect design choices to operations, SLAs, and audits. Teams can define measurable acceptance criteria-throughput, latency, packet loss-and tie them to specific controls, including error control strategies and duplex settings. Documenting full duplex, half duplex configurations alongside capacity estimates and cabling standards clarifies risk, avoids autonegotiation issues during cutovers, and supports vendor compliance checks. The same artifact drives test plans that trace defects to their layer of origin, speeding root-cause analysis during incident response and change windows.
This approach benefits common initiatives such as WAN modernization, data center migrations, M&A network integration, and OT/IoT segmentation. It also improves onboarding by giving operations, security, and procurement a shared reference for runbooks, performance baselines, and monitoring thresholds aligned to the OSI stack.
Proposal Kit can streamline these outcomes by assembling consistent, traceable documents, generating budgets with automated line-item quoting, and using its AI Writer to write supporting procedures and layer-specific checklists drawn from an extensive template library.
How to write my Open Systems Interconnection Reference Model Form document
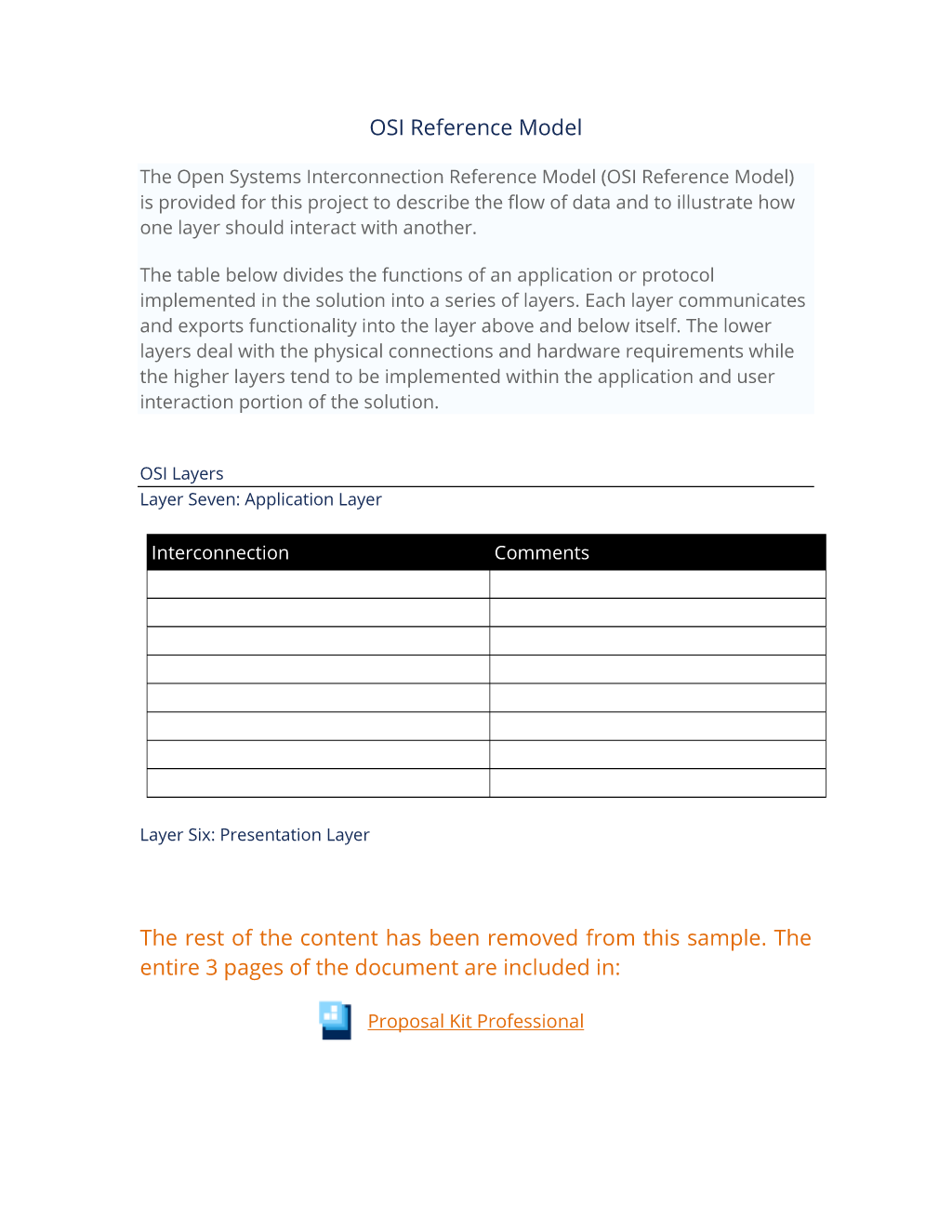
OSI Reference Model
The Open Systems Interconnection Reference Model (OSI Reference Model) is provided for this project to describe the flow of data and to illustrate how one layer should interact with another. The table below divides the functions of an application or protocol implemented in the solution into a series of layers. Each layer communicates and exports functionality into the layer above and below itself. The lower layers deal with the physical connections and hardware requirements while the higher layers tend to be implemented within the application and user interaction portion of the solution.
OSI Layers
Layer Seven: Application Layer
Interconnection Comments
Layer Six: Presentation Layer
Interconnection Comments
Layer Five: Session Layer
Interconnection Comments
Layer Four: Transport Layer
Interconnection Comments
Layer Three: Network Layer
Interconnection Comments
Layer Two: Data Link Layer
Interconnection Comments
Layer One: Physical Layer
Interconnection Comments
Repeat for each protocol needing a description – or combine all protocols by their layers into a single table per layer.
The editable Open Systems Interconnection Reference Model Form document - complete with the actual formatting and layout is available in the retail Proposal Kit Professional.
20% Off Discount
 4.7 stars, based on 849 reviews
4.7 stars, based on 849 reviews Ian Lauder has been helping businesses write their proposals and contracts for two decades. Ian is the owner and founder of Proposal Kit, one of the original sources of business proposal and contract software products started in 1997.
Ian Lauder has been helping businesses write their proposals and contracts for two decades. Ian is the owner and founder of Proposal Kit, one of the original sources of business proposal and contract software products started in 1997.By Ian Lauder
 Published by Proposal Kit, Inc.
Published by Proposal Kit, Inc.We include a library of documents you can use based on your needs. All projects are different and have different needs and goals. Pick the documents from our collection, such as the Open Systems Interconnection Reference Model Form, and use them as needed for your project.


 Cart
Cart
 Get 20% off ordering today:
Get 20% off ordering today:  Facebook
Facebook YouTube
YouTube Bluesky
Bluesky Search Site
Search Site