How to write your Security Breach Report Form
We include this 6 page template with IT/Software/Hardware Contract Pack and the Proposal Kit Professional. You will get more content and software automation for data merging, managing client documents, and creating proposals with line item quoting with a Contract Pack or the Professional.
 DOWNLOADABLE, ONE-TIME COST, NO SUBSCRIPTION FEES
DOWNLOADABLE, ONE-TIME COST, NO SUBSCRIPTION FEES What Our Clients Say
What Our Clients SayBefore I used the Web Freelancer Contract Pack, I would often find myself forgetting to include items in my agreements with clients that lead to frustration, usually on my part. This contract pack has allowed me to keep a consistent look to my client documents, and helped me be more proactive and helpful to my clients, by covering all of the bases I need to cover."
Webbit Media LLC.
1. Get IT/Software/Hardware Contract Pack or the single template that includes this business contract document.
We include this contract in editable Word format that can be customized using your office software.
2. Download and install after ordering.
Once you have ordered and downloaded your template or pack, you will have all the content you need to get started.
3. Customize the contract template with your information.
You can customize the contract document as much as you need. If you get a Contract Pack or Professional Bundle, you can also use the included Wizard software to automate name/address data merging.
Use cases for this template
Malware outbreak at Blue Harbor Payments
The Challenge
Just after a product launch, Blue Harbor Payments watched endpoints lock up and card-processing queues stall, leaving the Point of Contact unsure how to classify the event and racing to file the security incident report while executives demanded clarity.
The Solution
They used the incident report template to structure facts, witnesses, affected systems, and corrective actions, then turned to Proposal Kit to create supporting materials-an executive briefing, a remediation proposal with automated line-item quoting for cleanup and replacement assets, and a consumer notification plan drafted with the AI Writer-without altering the legal contract itself.
The Implementation
The POC captured discovery details and evidence, Security mapped containment steps, and the Proposal Kit's document assembly produced a uniform packet; the AI Writer generated status updates and a technical appendix, while line-item quoting priced EDR licenses, forensic hours, and hardware so finance could vet the budget the same day.
The Outcome
Blue Harbor contained the malware within hours, briefed stakeholders with consistent documents, and submitted an insurance-ready packet that sped reimbursement and funded hardening measures tied directly to the quoted items.
Willow Grove Human Services handles a privacy scare
The Challenge
A caseworker at Willow Grove accidentally emailed a spreadsheet with a person's health intake notes to a community list, triggering an inadvertent disclosure that threatened consumer trust and required swift documentation and outreach.
The Solution
The team completed the incident report to record timeline, systems touched, and communications, then used Proposal Kit to build a privacy impact assessment, outreach scripts, and FAQs for consumers via the AI Writer, and a staff retraining plan; automated line-item quoting, estimated encryption tools, mailbox auditing, and awareness sessions.
The Implementation
HR and Security coordinated evidence and corrective actions inside the report, while Proposal Kit assembled a briefing book; the AI Writer produced plain-language notices and a manager's Q&A, and the quotes packaged costs for leadership approval pursuant to internal policy.
The Outcome
Notifications went out the same day, the board approved targeted controls and training based on the quoted plan, and Willow Grove restored confidence with a transparent, well-documented response.
Ironcrest Fabrication faces a break-in and data theft
The Challenge
After a weekend break-in, Ironcrest discovered stolen laptops and a compromised system tied to a vendor connection, forcing the company to record physical and digital intrusions and coordinate with state police while keeping production online.
The Solution
They used the incident report to log locations, witnesses, and effects on services, and relied on Proposal Kit to craft a vendor remediation plan, a board-ready incident study, and a tabletop exercise outline with the AI Writer, plus automated line-item quoting for cameras, badging, and managed detection services.
The Implementation
The POC submitted a complete report with evidence custody notes; Proposal Kit assembled a professional packet, the AI Writer produced an operations continuity memo and exercise playbook, and quoted detailed capital and subscription costs so procurement could act quickly.
The Outcome
Ironcrest stabilized systems, accelerated vendor fixes, and secured funding for upgraded controls, all supported by consistent documents that turned a chaotic event into an organized, auditable recovery.
Abstract
This incident report form is a structured tool for documenting security events so an organization can assess impact, coordinate response, and record conclusions. A designated Point of Contact completes the form and files it with Security and Human Resources on a need-to-know basis. The form captures a concise summary and then expands into details that guide investigation and resolution.
The submission requires basic facts, witness names, and the type of event, including data breach, malware, theft, compromised systems, or physical intrusion. It records where the intrusion occurred, who to contact, and the effect on operations, such as unauthorized access, loss of data, service interruption, or damage. If you are unsure how to describe an item, the POC may request assistance before they submit the report, whether online or by other means.
Operational sections drive a thorough review. You identify systems affected, explain how the incident was discovered, and outline communications made and still pending. You log evidence gathered, who gathered it, and where it is stored.
You then describe the incident response workflow, personnel roles, corrective actions taken, and incident resolution. The conclusions summarize root cause, precautions, business impact on employees and consumers, estimated costs, and further actions. Attachments and an addendum can be included, pursuant to company policy.
When the incident involves health information, human services data, or the inadvertent disclosure of a person's identifying details, the entity may need to notify outside parties per applicable rules. That can include regulators or law enforcement, such as state police agencies (for example, New York State Police or York State Police). The form's evidence and communication sections help maintain the chain of custody and document required notices without offering legal advice.
Common use cases include an IT team responding to a ransomware outbreak, a retailer reporting theft of laptops, a clinic documenting unauthorized access to health records, or a nonprofit recording a physical break-in. The same workflow supports small businesses as well as larger enterprises.
Proposal Kit can streamline creating this report and related materials with document assembly, automated line-item quoting for remediation estimates, an AI Writer to build supporting documents, and an extensive template library. Teams can adapt the templates quickly, improving consistency and ease of use across security incident submissions.
Beyond documenting a single event, this report functions as a governance tool. It sets role-based distribution on a need-to-know basis, protects evidence, and promotes consistent metrics such as time to detect, contain, and recover. It also supports insurance claims, internal audit reviews, and vendor management when a third-party entity or contractor touches affected systems.
When an organization handles health or human services data, the same structure helps separate operational facts from privacy impact so leaders can plan consumer notifications and coordinate outreach if an inadvertent disclosure involves a specific person. If circumstances warrant law enforcement involvement, the package can include contact details for state police agencies, such as the New York State Police or the New York State Police, pursuant to internal policy.
The form also fits modern workflows. Teams can submit an online submission or use a printed packet. If staff are unsure how to classify an incident, the Point of Contact can request assistance before they submit, ensuring accuracy.
You can attach an addendum for tabletop exercise results, vendor forensics, cost breakdowns, or communications prepared for consumers and employees. Clear sections for discovery, response, and corrective actions make it easier to brief executives and align budgets with remediation tasks.
Proposal Kit helps teams operationalize this process. Its document assembly streamlines building uniform incident packets with consistent language. Automated line-item quoting makes it faster to estimate remediation, replacement hardware, and service credits.
The AI Writer can write supporting documents such as status updates, witness statement forms, and consumer-facing summaries, while the extensive template library accelerates checklists, playbooks, and addendum pages. Together, these tools make it easier to produce complete, professional submissions that keep stakeholders aligned without adding friction to the response.
Further value comes from how this report standardizes scoring and escalation. By assigning severity, impact, and containment status, leaders can align response targets with business continuity goals and SLAs. Clear RACI-style ownership reduces delays and avoids duplicated work between Security, HR, and operations.
Time-stamped entries, consistent terminology, and chain-of-custody notes strengthen evidentiary quality, which supports cyber insurance claims, procurement disputes, and internal control audits. A defined retention schedule and litigation hold flags help preserve records when an incident may affect an entity's contractual obligations or pending claims.
The template also enables trend analysis. Aggregating submissions over time reveals hotspots by facility, vendor, or system and highlights training gaps. For organizations handling health and human services data, adding a privacy impact field separates operational facts from consumer outreach steps when an inadvertent disclosure involves a specific person. A prebuilt section for third-party coordination captures vendor notifications, pursuant to contract terms, and documents when upstream or downstream providers were engaged.
Operational maturity improves when the same format is used for tabletop exercises and post-incident reviews. Lessons learned convert into new controls, budget requests, and policy updates. Executive summaries drawn from the form feed board dashboards with metrics such as mean time to detect and recover, estimated cost, and residual risk.
Online submission options help remote teams collaborate, while an addendum can attach forensics, cost models, and consumer messaging plans. If staff are unsure about classification or containment, a request for assistance pathway directs questions early, which prevents missteps and improves outcomes.
Proposal Kit supports this lifecycle by letting teams tailor incident templates to departments, assemble uniform packets quickly, and generate related documents with the AI Writer. Automated line-item quoting helps estimate remediation, replacement assets, and services. Its extensive template library shortens turnaround and improves consistency, making it easier for any organization to produce complete, professional submissions without adding process overhead.
How do you write a Security Breach Report Form document? - The Narrative
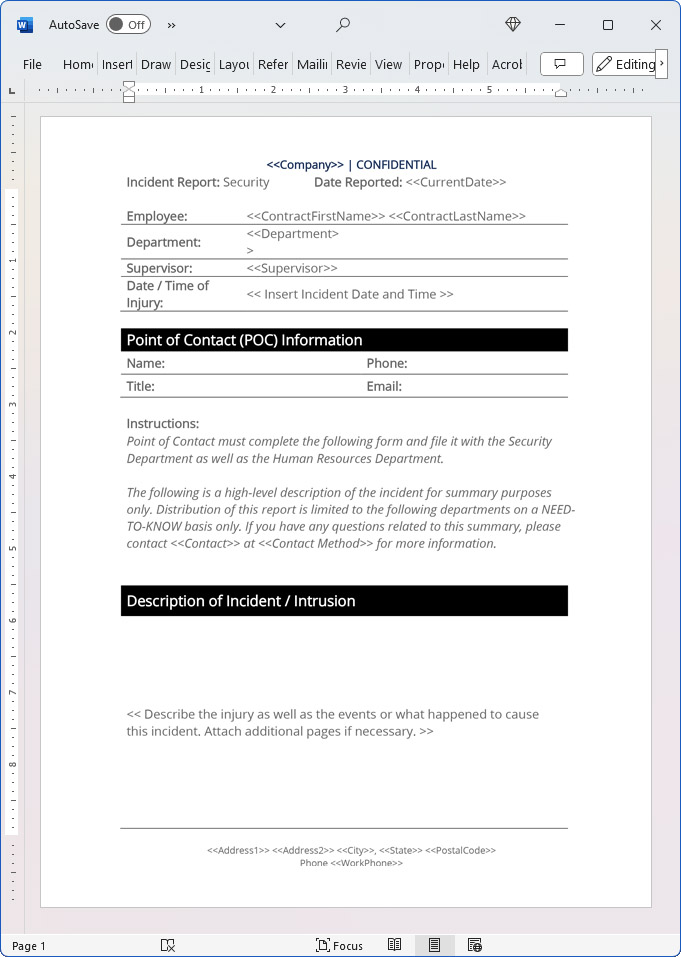
Incident Report: Security Date Reported: Current Date. Employee: First Last Department: Department Supervisor: Supervisor Date / Time of Injury: Insert Incident Date and Time. Point of Contact (POC) Information Name: Phone: Job title of signator, authorized signature or signer.
Point of Contact must complete the following form and file it with the Security Department as well as the Human Resources Department. The following is a high-level description of the incident for summary purposes only. Distribution of this report is limited to the following departments on a NEED-TO-KNOW basis only.
If you have any questions related to this summary, please contact at method for more information. Description of Incident / Intrusion Describe the injury as well as the events or what happened to cause this incident. Attach additional pages if necessary.
Witnesses Did anyone witness the incident or evidence of the incident after it occurred?
Yes ? No ? Name(s) of Witnesses:
Type of Intrusion (Please check all that apply) Intrusion ? Data Breach ? Theft ? Malware/Trojan/Virus ? Compromised System ? Physical Intrusion ? Other ?
Intrusion Location and Information: (Name, Address, Phone if applicable) Notes:
Effect of Intrusion (Please check all that apply. Loss of Data ? Unauthorized Access of Data ? Theft ? Degradation of Service(s) ? Interruption of Service ?
Physical Damage to System(s) ? Unauthorized Escalation of Privileges ? Physical Intrusion ? Other ?
Additional Information:
Systems Affected
Insert the systems this intrusion affected.
Intrusion Discovery
Describe how, where, and by whom this intrusion was first detected.
Communication / Notification
Describe the notifications and communication that were carried out at every step. Also describe any initial notification, follow-up, resolutions and communication(s) that still need to be made at this stage.
Evidence and Documentation
Describe the evidence and documentation, logging, files, etc., that have been gathered at each step, and indicate by whom they were gathered. Attach additional sheets if necessary.
Incident Response
Describe the work flow of the incident response, including personnel involved at each stage and all actions taken. Attach additional sheets if necessary. Corrective Action(s) Taken and Incident Resolution. Describe the corrective actions taken, including names of parties responsible for those actions, to address each system impacted by the intrusion.
Attach additional sheets if necessary.
Conclusion and Findings
Insert conclusions reached at this stage. Attach additional sheets if necessary.
Conclusions may include:
The root or proximate cause of this incident. Precautions that could have prevented this. The direct and indirect impact on the Company and its systems, customers, users, employees, etc. The estimated cost to investigate, respond to, and correct the intrusion.
The steps that have been taken to prevent the incident from happening again and to limit further interruption. The additional actions, research or communication that need to happen.
20% Off Discount
![]() Add To Cart This Word Template Only
Add To Cart This Word Template Only
 Add To Cart IT/Software/Hardware Contract Pack
Add To Cart IT/Software/Hardware Contract Pack
 Add To Cart Proposal Kit Professional Bundle
Add To Cart Proposal Kit Professional Bundle
 4.7 stars, based on 849 reviews
4.7 stars, based on 849 reviewsRelated Documents
How to Build a Legal Contract with Proposal Kit
This video illustrates how to create a legal contract using the Proposal Pack Wizard software. It also shows how to create a proposal with an invoice and contract at the same time.
Frequently Asked Questions
How do I customize this contract to fit my business needs?
Customizing this contract involves editing the document to include your business details, terms, and conditions. The templates are designed to be flexible, allowing you to insert your company's name, address, and other relevant information. You can modify clauses to reflect your unique business practices and legal requirements.
Is this contract compliant with laws and regulations?
The legal contract templates are written by legal professionals and designed to comply with current laws and regulations at the time of their writing. However, laws can vary by jurisdiction and change over time, so it's recommended to have your contract reviewed by a local attorney to ensure it meets all legal requirements specific to your region and industry. Templates are licensed as self-help information and not as legal advice.
Can I use the same contract for different clients or projects?
You can use the same contract for different clients or projects. The templates are versatile and easily adapted for various scenarios. You will need to update specific details such as client names, project descriptions, and any unique terms for each new agreement to ensure that each contract accurately reflects the particulars of the individual client or project.
What should I do if I encounter a clause or term I don't understand?
If you encounter a clause or term in the contract that you need help understanding, you can refer to guidance notes explaining each section's purpose and use. For more complex or unclear terms, it's advisable to consult with a legal professional who can explain the clause and help you determine if any modifications are necessary to suit your specific needs.
How do I ensure that the contract is legally binding and enforceable?
To ensure that the contract is legally binding and enforceable, follow these steps:
- Complete all relevant sections: Make sure all blanks are filled in with accurate information.
- Include all necessary terms and conditions: Ensure that all essential elements, such as payment terms, deliverables, timelines, and responsibilities, are clearly defined.
- Signatures: Both parties must sign the contract, and it is often recommended that the contract be witnessed or notarized, depending on the legal requirements in your jurisdiction.
- Consult a legal professional: Before finalizing the contract, have it reviewed by an attorney to ensure it complies with applicable laws and protects your interests.
 Ian Lauder has been helping businesses write their proposals and contracts for two decades. Ian is the owner and founder of Proposal Kit, one of the original sources of business proposal and contract software products started in 1997.
Ian Lauder has been helping businesses write their proposals and contracts for two decades. Ian is the owner and founder of Proposal Kit, one of the original sources of business proposal and contract software products started in 1997.By Ian Lauder
 Published by Proposal Kit, Inc.
Published by Proposal Kit, Inc.Disclaimers
Proposal Kit, Inc. makes no warranty and accepts no responsibility for the suitability of any materials to the licensee's business. Proposal Kit, Inc. assumes no responsibility or liability for errors or inaccuracies. Licensee accepts all responsibility for the results obtained. The information included is not legal advice. Names in use cases have been fictionalized. Your use of the contract template and any purchased packages constitutes acceptance and understanding of these disclaimers and terms and conditions.


 Cart
Cart
 Get 20% off ordering today:
Get 20% off ordering today: 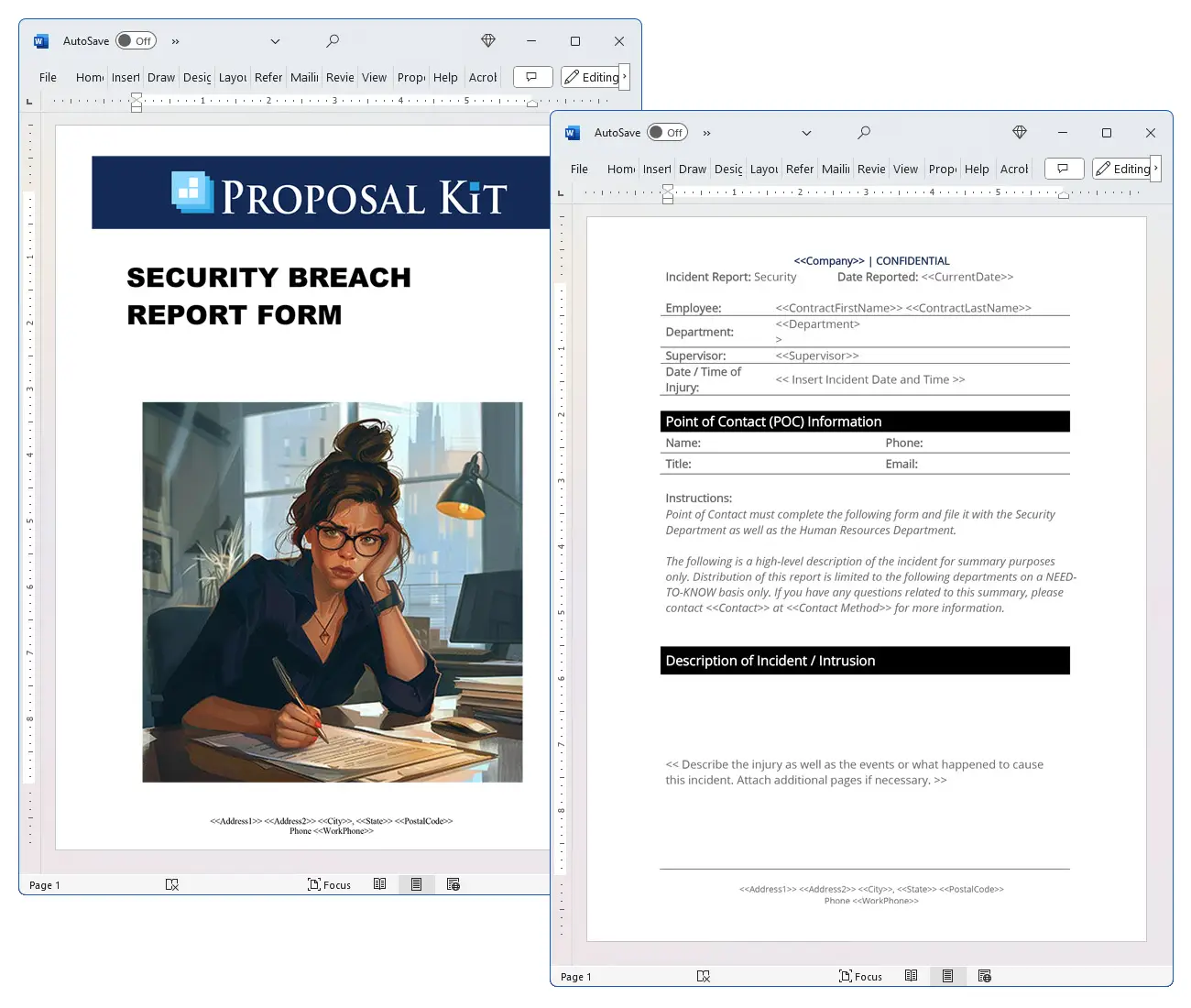
 Facebook
Facebook YouTube
YouTube Bluesky
Bluesky Search Site
Search Site