What is the Vulnerabilities chapter used for?
Proposal Kit Professional Bundle adds more design themes, all six Contract Packs,
a project management library, and Expert Edition software.
Illustration of Proposal Pack Financial #5
We include this Vulnerabilities chapter template in every Proposal Pack, along with thousands more. You assemble this chapter with others in various combinations to create custom-tailored business proposals, plans, reports, and other documents. Proposal Packs apply custom visual designs to the templates, giving the final documents a consistent professional finish.
 DOWNLOADABLE, ONE-TIME COST, NO SUBSCRIPTION FEES
DOWNLOADABLE, ONE-TIME COST, NO SUBSCRIPTION FEES
Overview of the Vulnerabilities Chapter
The Vulnerabilities chapter is an important component in a range of business proposal documents. It is specifically crafted to help outline and discuss any weaknesses or areas of risk associated with a project or operation. This chapter serves a purpose by allowing the proposal's author to demonstrate foresight and preparedness. Acknowledging and planning for potential vulnerabilities not only enhances the credibility of the proposal but also shows a proactive approach to risk management.
How is the Vulnerabilities Chapter Used?
In the structure of a business proposal, the Vulnerabilities chapter is used to transparently address any concerns that might impact the project's success. This may involve discussing technical flaws, operational weaknesses, financial risks, or external factors that could pose challenges to the project. By identifying these issues early in the proposal, solutions can be proposed in subsequent sections, thereby reinforcing the project's viability and securing the confidence of stakeholders or potential clients.
What is Included in the Vulnerabilities Chapter?
Typically, the Vulnerabilities chapter includes:
- A detailed identification of potential risks associated with the project.
- Analysis of the implications each vulnerability could have on the project's outcome.
- A preliminary discussion on possible mitigation strategies to address these vulnerabilities.
- References to data or case studies that support the identification of these vulnerabilities.
- Sometimes, visual aids such as charts or graphs to help illustrate the potential impact of these vulnerabilities.
Use Case Examples for the Vulnerabilities Chapter
The Vulnerabilities chapter can be adapted for various contexts within business proposals, including:
- Security Proposals: Identifying areas where security measures could be compromised.
- Protection Plans: Discussing vulnerabilities in systems meant to protect data or premises.
- Safety Protocols: Highlighting potential safety issues within a proposed operational change.
- Problem Analysis: For projects aimed at solving issues, outlining why previous solutions may have failed.
- Negative Impact Assessments: Evaluating the negative impacts of a project on the environment or community.
Key Takeaways
- The Vulnerabilities chapter is important for demonstrating risk awareness and management in proposals.
- It helps build trust with stakeholders by being upfront about potential risks.
- This chapter not only identifies risks but also sets the stage for proposing solutions.
- It is and can be adapted to a wide range of proposals, from security to environmental impact assessments.
- Effective use of the Vulnerabilities chapter can significantly enhance the persuasiveness of a business proposal.
Illustration of Proposal Pack Lawn #3
 What Our Clients Say
What Our Clients SayAn excellent product for writing proposals. I have used this since 2000."
Lake Piso Technologies
 4.7 stars, based on 849 reviews
4.7 stars, based on 849 reviewsRelated Chapters
Samples Using the Vulnerabilities Chapter
Document Layouts Using the Vulnerabilities Chapter
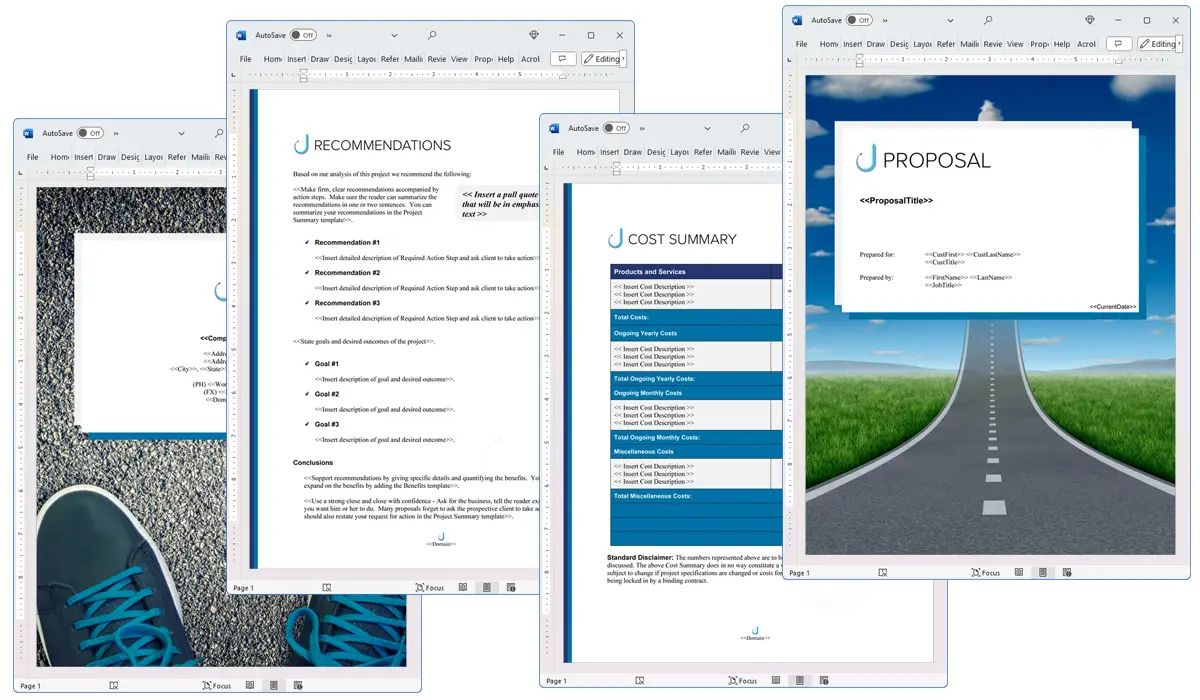
The Vulnerabilities chapter and other chapters are integrated into a Word document as illustrated here in the Proposal Pack Classic #21 design theme. There are hundreds of design themes available, and every design theme includes the Vulnerabilities chapter template.
A proper business proposal will include multiple chapters. This chapter is just one of many you can build into your proposal. We include the complete fill-in-the-blank template in our Proposal Pack template collections. We also include a library of sample proposals illustrating how companies in different industries, both large and small, have written proposals using our Proposal Packs. This template will show you how to write the Vulnerabilities.
We include a chapter library for you to build from based on your needs. All proposals are different and have different needs and goals. Pick the chapters from our collection and organize them as needed for your proposal.
Using the Proposal Pack template library, you can create any business proposal, report, study, plan, or document.
The Wizard software includes an AI Writer, which will write the content of this and any other chapter of your document. Use the AI Writer to do the heavy lifting, writing the first draft of your proposal or business document in minutes.
 Ian Lauder has been helping businesses write their proposals and contracts for two decades. Ian is the owner and founder of Proposal Kit, one of the original sources of business proposal and contract software products started in 1997.
Ian Lauder has been helping businesses write their proposals and contracts for two decades. Ian is the owner and founder of Proposal Kit, one of the original sources of business proposal and contract software products started in 1997.By Ian Lauder
 Published by Proposal Kit, Inc.
Published by Proposal Kit, Inc.

 Cart
Cart
 Facebook
Facebook YouTube
YouTube Bluesky
Bluesky Search Site
Search Site